Virus Scanning Protection¶
Last updated: Jul 29, 2025
NOTE: This guide is for Access Anywhere 2402.1 and above. For versions before 2402.1 see Antivirus-Pre2402.1
Access Anywhere prevents the downloading and sharing of malicious files through a ‘scan on write’ approach. As files are uploaded they are scanned. If a virus is detected, the upload fails, and an error is returned immediately to the user or application.
The audit log (for add/update) captures successful and unsuccessful scans and uploads:
File solution-brief.pdf uploaded to My Cloud files/mybucket. Scanned with antivirus ClamAV 0.99.2/24143/
ClamAV is the officially supported virus scanner available for use with Access Anywhere. ClamAV is a high performance multi-threaded daemon supporting many file formats including file and archive unpacking.
In High Availability environments each appliance serving web traffic will be required to run a local ClamAV service. Files added outside of Access Anywhere, directly to the external storage and discovered through provider synchronization, are not scanned.
Files larger than 1.5GB will be uploaded without being scanned, and only the first 1.5GB of files that expand during scanning to more than 1.5GB will be scanned.
Service Configuration¶
ClamAV must first be enabled and configured on each web node.
1. Start and Enable ClamAV¶
SSH to the appliance as user smeconfiguser, then become root
su -
Start the Antivirus container. It will automatically restart on reboots:
cd /var/www/smestorage/containers/clamav
docker compose up -d
Next verify that it is running and enabled: NOTE: It might take 60+ seconds for the health to change from starting to healthy
# docker compose ps
NAME IMAGE COMMAND SERVICE CREATED STATUS PORTS
clamav registry.storagemadeeasy.com/clamav/clamav:1.4.3-3 "/init" clamav 38 seconds ago Up 37 seconds (healthy) 3310/tcp, 7357/tcp
2. Verify Appliance Integration with ClamAV¶
The appliance configuration file can be found at:
/var/www/smestorage/public_html/config.inc.php
Verify that the settings below are configured as shown:
var $enableantivirus = 1;
var $clamavsocketpath = '/var/clamav/clamd.sock';
Enabling ClamAV for Organizations¶
The virus scanning of uploads is a configuration option for organizations. The option is available when added to the user package.
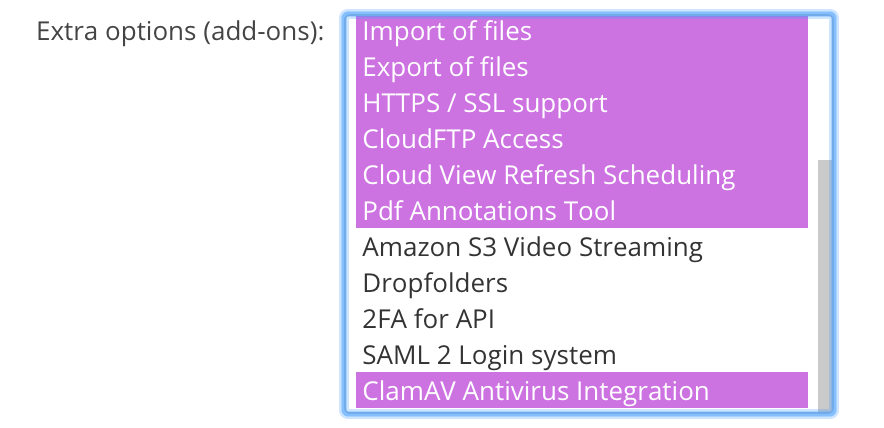
1. Adding the ClamAV Option to a User Package¶
To make the ClamAV available as a configuration option for an organization tenant the feature must be added as an 'Extra option' in the User Package.
To make this change, login as the Appliance Administrator (appladmin). From the Main menu (the hamburger icon top right) select 'User Packages’. For the package you want to change select Edit (the pencil icon). Once you’ve selected 'ClamAV Antivirus Integration' choose Save.
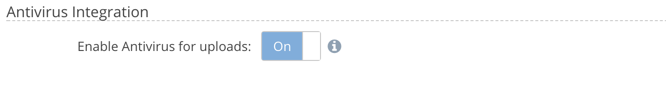
2. Enabling Antivirus Scanning¶
An Organization Administrator can enable virus scanning for uploads under Organization > Policies > Security:
Troubleshooting¶
Checking ClamAV Service Logs¶
Once started the ClamAV service will generate log data.
To review the ClamAV logs
docker logs -f clamav
Configuration¶
ClamAV configuration settings can be found at:
/var/www/smestorage/containers/clamav/clamd.conf
Checking Virus Signatures are Fresh¶
The Freshclam application updates the antivirus signature database. It is preinstalled on the appliance and by default is scheduled to run once an hour.
To verify Freshclam has been running successfully check the definition version and date
# docker exec -it clamav clamd --version
ClamAV 1.4.3/27713/Mon Jul 28 08:36:30 2025
In the output above ClamAV is running version 1.4.3 with a virus definition version of 27713 which was published on Mon Jul 28 08:36:30 2025
Error: Socket Operation Failed¶
If the ClamAV service is not running when the user uploads a file the user may see the following message:
Socket operation failed: No such file or directory (SOCKET_ENOENT)
Checking Virus Scans¶
Verify scans are operational through the audit trail. The policy “Audit File add/update” must be enabled by an administrator under Policies > Security > Audit > Events.
File solution-brief.pdf uploaded to My Cloud files/mybucket. Scanned with antivirus ClamAV 0.99.2/24143/
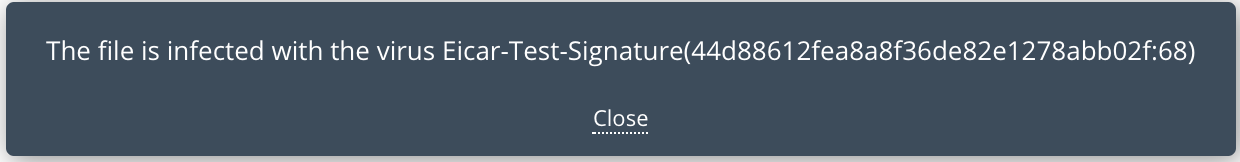
For a positive match the log looks like:
EICAR-testfile.txt failed to upload to myprovider/mybucket/myfolder . Antivirus ClamAV detected Eicar-Test-Signature(44d88612fea8a8f36de82e1278abb02f:68) infection. ClamAV version ClamAV 0.99.2/24211/
For a test virus file see https://en.wikipedia.org/wiki/EICAR_test_file.